Introduction
Last week, on September 21, Microsoft announced that Windows Copilot will begin to roll out to Windows 11, starting September 26.
Curious to know more on managing Windows Copilot, I dug into the various documentation on the subject, as well as researching on Twitter.
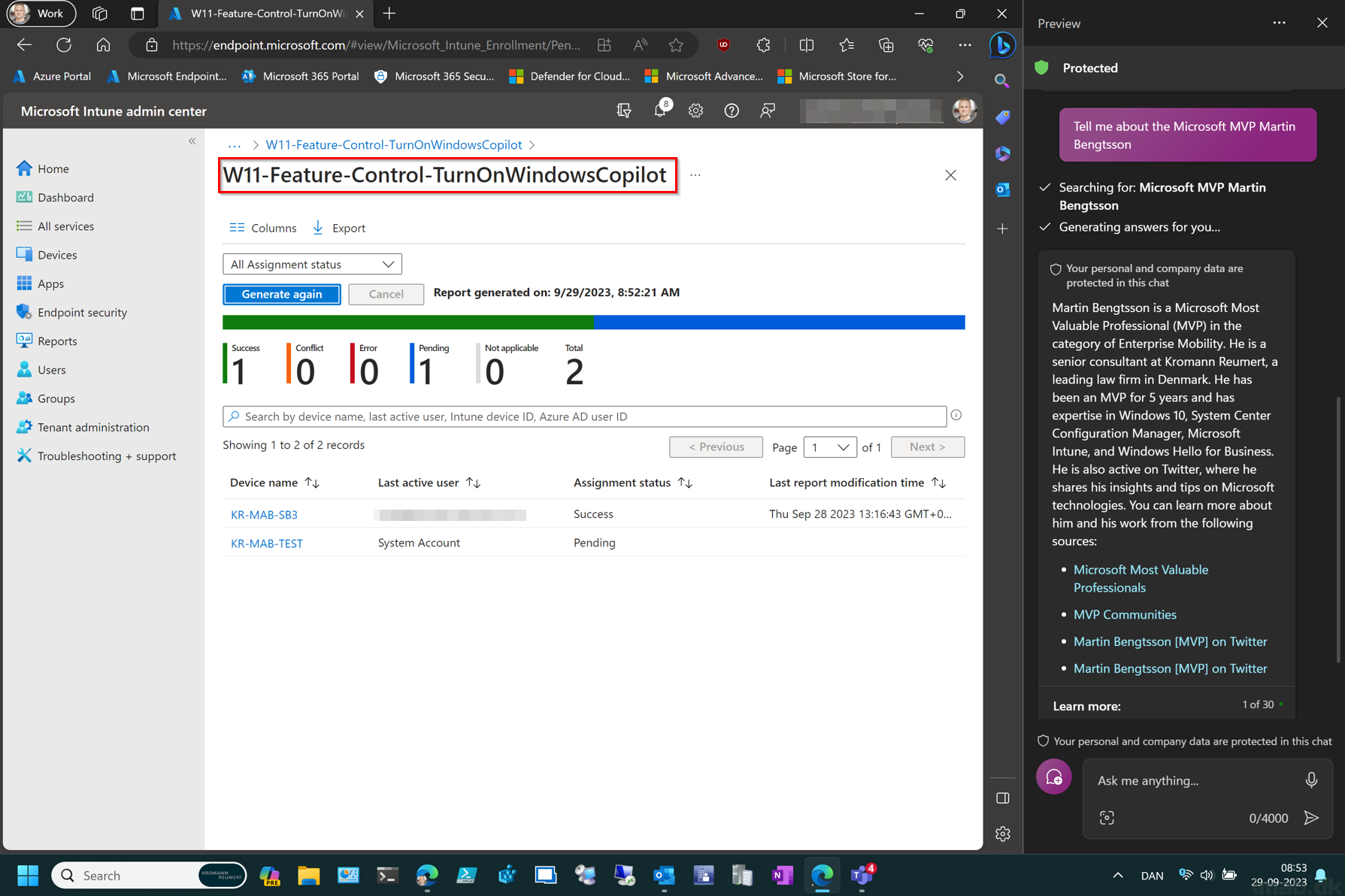
I managed to get to enable Windows Copilot on my Intune-managed Windows 11 device. Note that I’m located in Europe, and some documentation suggests that Windows Copilot isn’t available here just yet.
This post serves as notes from the field. 🙂