Introduction
Active Directory is a prime target for attackers – and for most organizations something that’s considered the crown jewels. This is due to Active Directory still being the bread and butter for most organizations in regard to authentication and authorization.
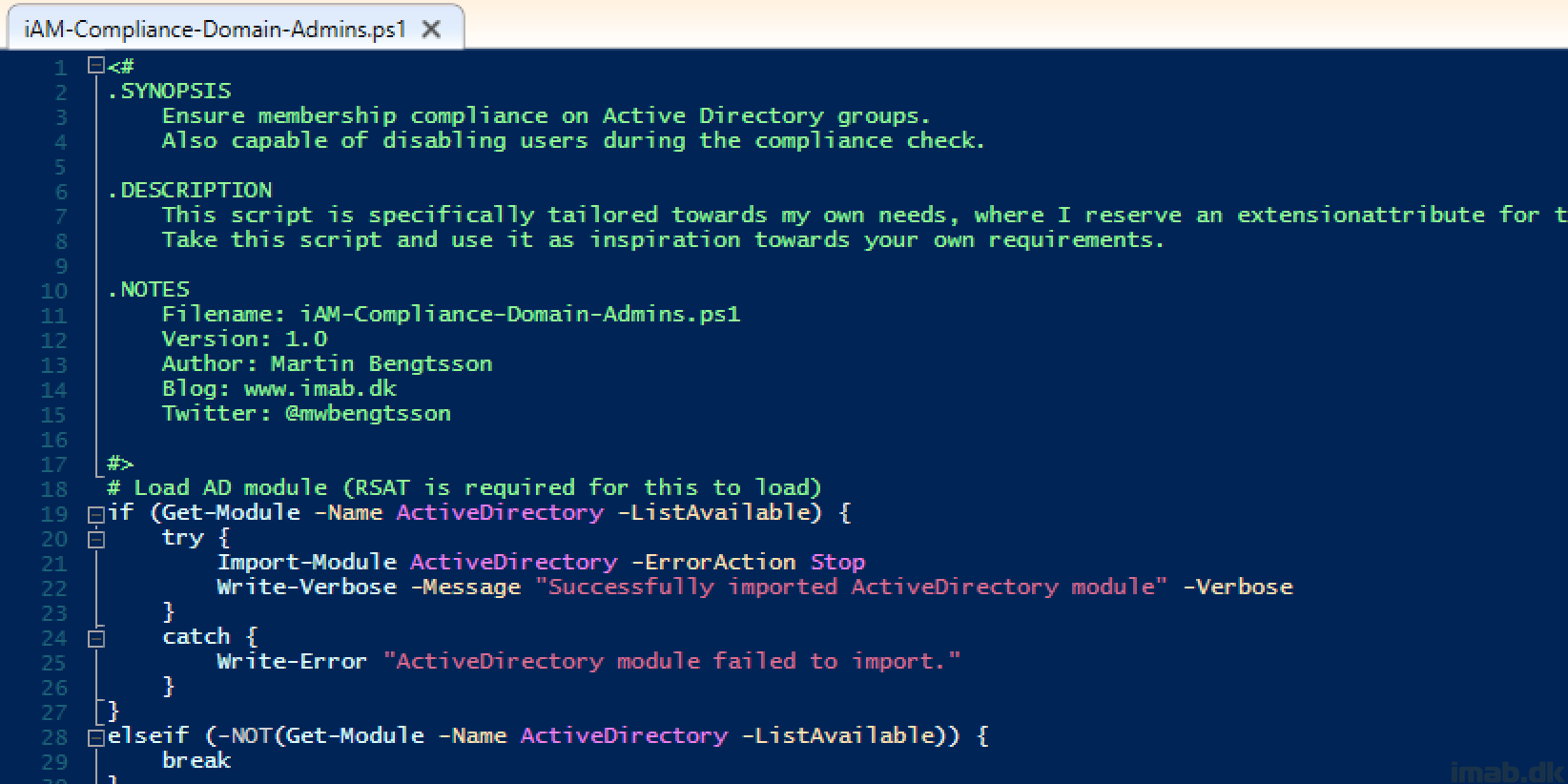
When it comes to security, automation is your best friend and keeping a close eye on privileged group membership should be on top of your list.
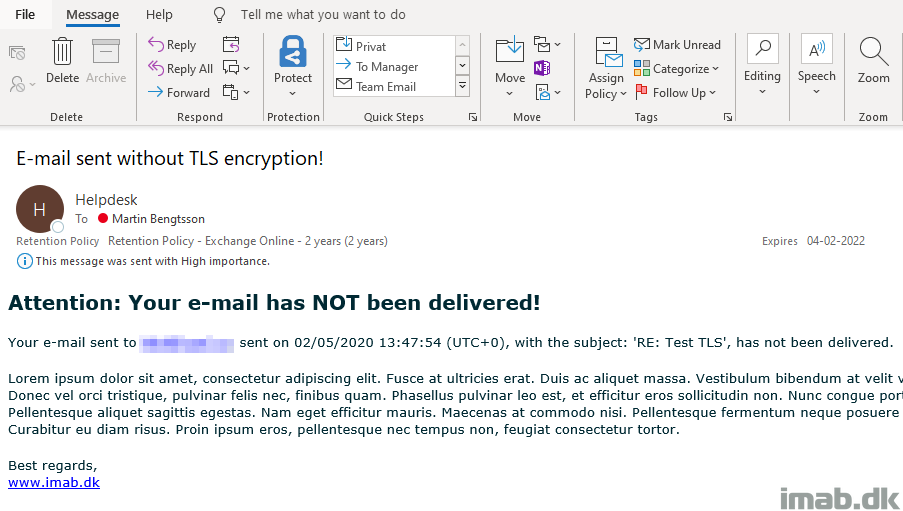
This post will walk you through, how you can make sure no unwelcome objects make their way into privileged groups in on-premises AD, by leveraging Microsoft Sentinel and its option to run playbooks automated.
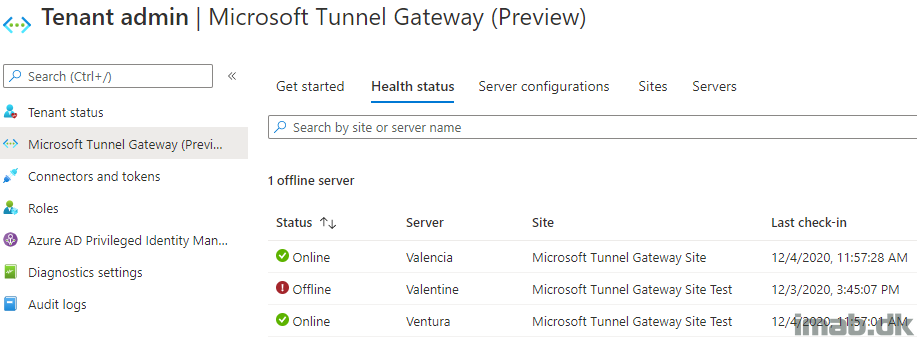
This breaks down to Microsoft Sentinel generating an alert, which triggers the associated Playbook, which triggers a Logic app, which triggers a Runbook in an Automation Account, which ultimately runs a PowerShell script on an on-premises server.
Big shout out to my colleague Christian Frohn Petersen who assisted in setting up the prerequisites for this solution. 🙂