Update: Post and script moved to https://www.imab.dk/lenovo-bios-configurator/
I have no idea if this is something that has already been created out there, but I figured I’d do it anyway. Mostly because Powershell, I need the practice and I needed the ability to easily modify the BIOS in our Lenovo environment.
The script is inspired by the original VB script from Lenovo, which roughly does the same as my Powershell script. Lenovos script and documentation can be reached from this link (https://support.lenovo.com/dk/en/solutions/ht100612). However, it’s VB and it gives me shivers, so Powershell to the rescue.
The script is still work in progress, as it doesn’t hold all the abilities as the original Lenovo script, but I prioritized the ability to turn on/off following: Virtualization, SecureBoot, PrebootUSB-C/Thunderbolt and TPM.
You basically just run the script with parameters. Example: LenovoBIOSManagement.ps1 -EnableTPM -EnableSecureBoot -DisableVirtualization -Restart
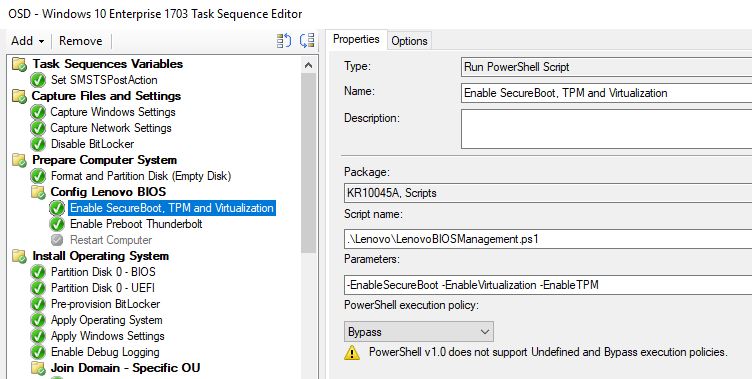
An example from the use in my recent Windows 10 Task Sequence. The step is run prior to formatting the disk in WinPE. I have a condition on the step, to only run if a Lenovo laptop.
Enable Preboot Thunderbolt is separated as a single step, as it’s currently only the most recent Lenovo laptops which has this ability: T470s, X1 Yoga 2nd generation etc., and therefore has a condition to only run if such model is being deployed.
I’d appreciate any feedback. I’m by no means any Powershell champ, but I’m still learning – and willing to learn 🙂
Thanks!
If I use the cmdlet to enable secure boot, will it also switch to UEFI only boot or is this a prerequisite?
As far as my testing goes, SecureBoot always enables UEFI on all the Lenovo laptops I’ve worked with 🙂
Hi Martin,
This is great. I am going to test this script very soon and provide you feedback. In the meantime do you have the script for enabling Intel PTT from Discrete TPM under Security chip selection and also a script to set supervisor password? we need this in our environment for Bitlocker encryption to work properly?
Appreciate any help from you 🙂
Hi Martin,
I am trying this script on a password (BIOS/Supervisor password) enabled laptop and script exits with “Security password count exceeded”. Is there a way to access BIOS with password or removes BIOS first and then change the settings?
Thank you,
Vinodh.
Hi,
I am experiencing the issue with enabling the secure boot before the partition of the disk. Could you please provide the partition information before the PowerShell. i am referring to format and partitioin (Empty) disk information
Hi, sure. This is just a quick partitioning and format of the disk (else there won’t be any available space for the powershell to run from). The step is also mentioning in details here: https://www.imab.dk/converting-from-bios-to-uefi-with-powershell-during-osd-using-configmgr/
Hi Martin,
Thanks a lot, it is working in two models. i will perform further test and update the status.
Thanks a lot for your wonderful support.
Hello Martin,
I have not tried enable secure boot with your powershell script but I used this way:
https://thinkdeploy.blogspot.com/2017/01/thinkpadthinkcentre-bios-to-uefi.html#comment-form
I enable Secure Boot and the machine boot up as UEFI and format GPT disk with no problem.
My problem is that, when the Task Sequence is done, in windows under system information Secure Boot is still Off.
I solved this manually by going in to the BIOS change Security Boot mode from “Setup Mode” to “Standard Mode”. This was done by manually pressing “Restore Factory Keys”. Before I did this Secure Boot was enabled in BIOS. But after this action when I restarted the machine and checked system information in windows 10, Secure Boot State=on.
So my question is, how do you automatically also do a “Restore Factory Keys” during a task sequence?
Or was this solved with your powershell script? Im going to try it tomorrow anyway :=)
So my task sequence is solving my BIOS2UEFI switch so I can change from MBR to GPT during a fresh install of a machine, but it will not enable Secure Boot itself all the way in windows. This happen on a Lenovo X1 that have been used with Windows 7 for a while.
Hi Andreas,
I know this question was asked a long time ago, but maybe you have figured out in the meantime if it is actually possible to “Restore Factory Keys” from a SCCM Task Sequence on Lenovo devices?
Hi Martin,
This looks like wonderful, wonderful work! Thank you for your time and effort!
I would like to use your script in a Task Sequence for an In-Place OS upgrade (from Win 7 to Win 10), if possible? I do not want to format the disk, I will call MBR2GPT to change the disk type (I know this works in a TS already). Would I run your script BEFORE or AFTER I call MBR2GPT? Also, can your script pass the BIOS password as part of the variables, like the Lenovo VBS can? If so, I’m a happy bunny!
Thanks in advance!
Dave
Hi Dave, the script should run fine during an in place upgrade. The script can run during WinPE or in FullOS. The order in when you run the script shouldn’t matter at all. I’m afraid that I haven’t included anything in regards to the BIOS password as we don’t have that in our environment, but it’s been discussed lately, so I might look into it soon 🙂 Thanks.
Is there a way to use the -supervisorpass parameter to attempt to pass multiple passwords? My environment has 3 different passwords depending on the end users region
Hey, I would have to revisit my script to fully answer that, but I initially think it would be a bad idea to pass a wrong password on purpose to a given device. If a wrong password is entered, I have seen that you are temp. locked out and need to shut down the device in order to be able to pass the correct password.