Introduction
Really short post, just to illustrate the possible privileges of being a Configuration Manager admin and having the ConfigMgr client installed on a Domain Controller.
While this might be stating the obvious for some people, I think it deserves a mention regardless.
This dictates a proper tiering model, especially around your Domain Controllers, making sure that Configmgr Admins does not have access to Domain Controllers and vice versa, but also to treat your ConfigMgr environment as tier0.
Configuration Manager
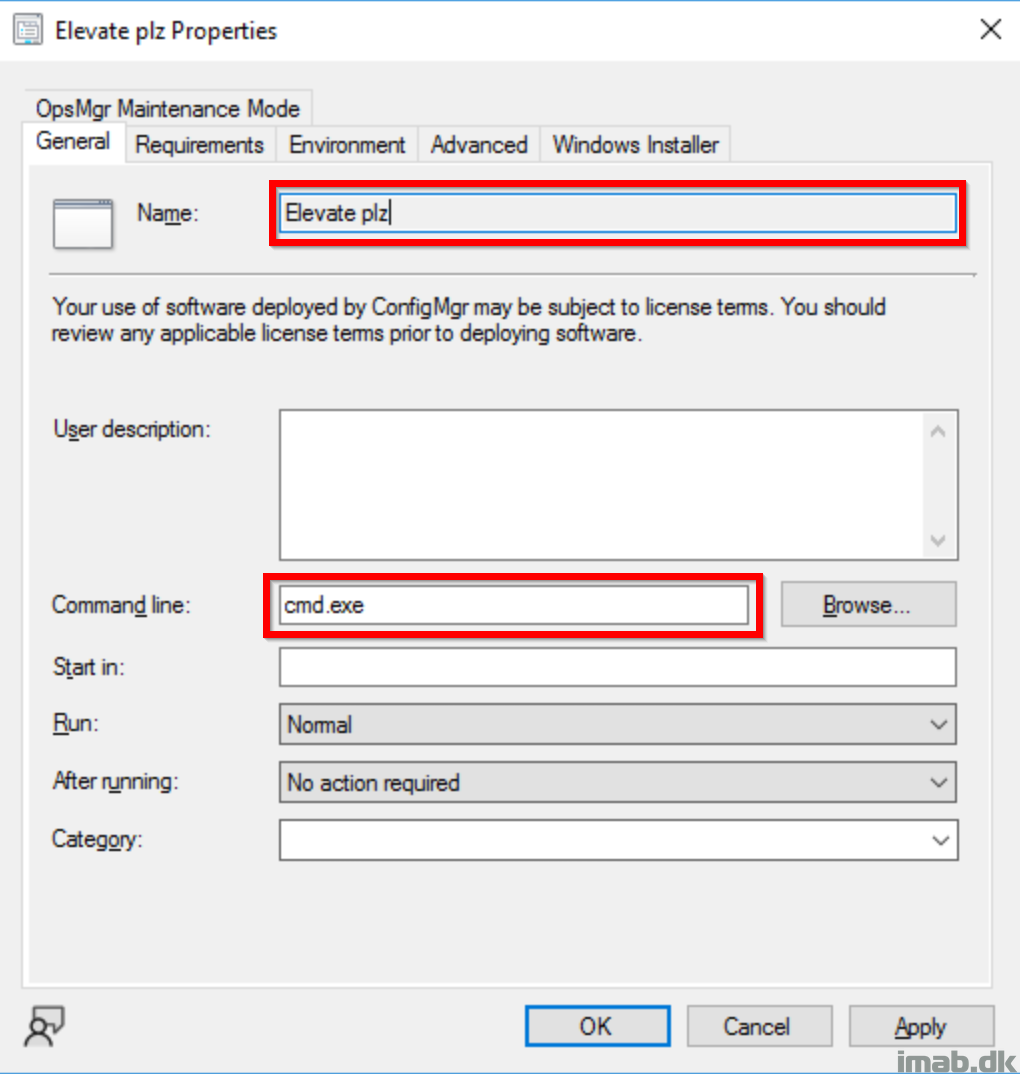
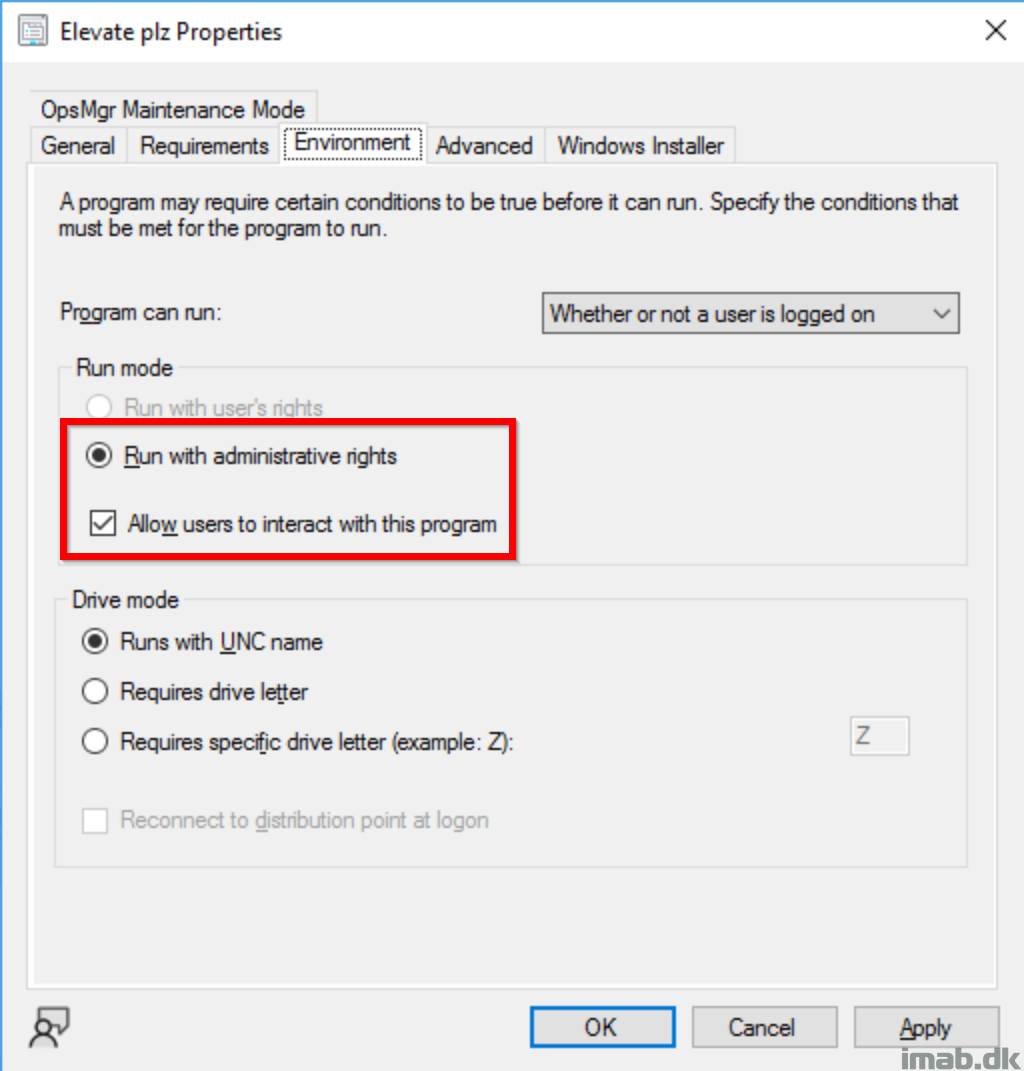
This is the simple program, I used to create an elevated and interactive cmd.exe session.
SYSTEM context
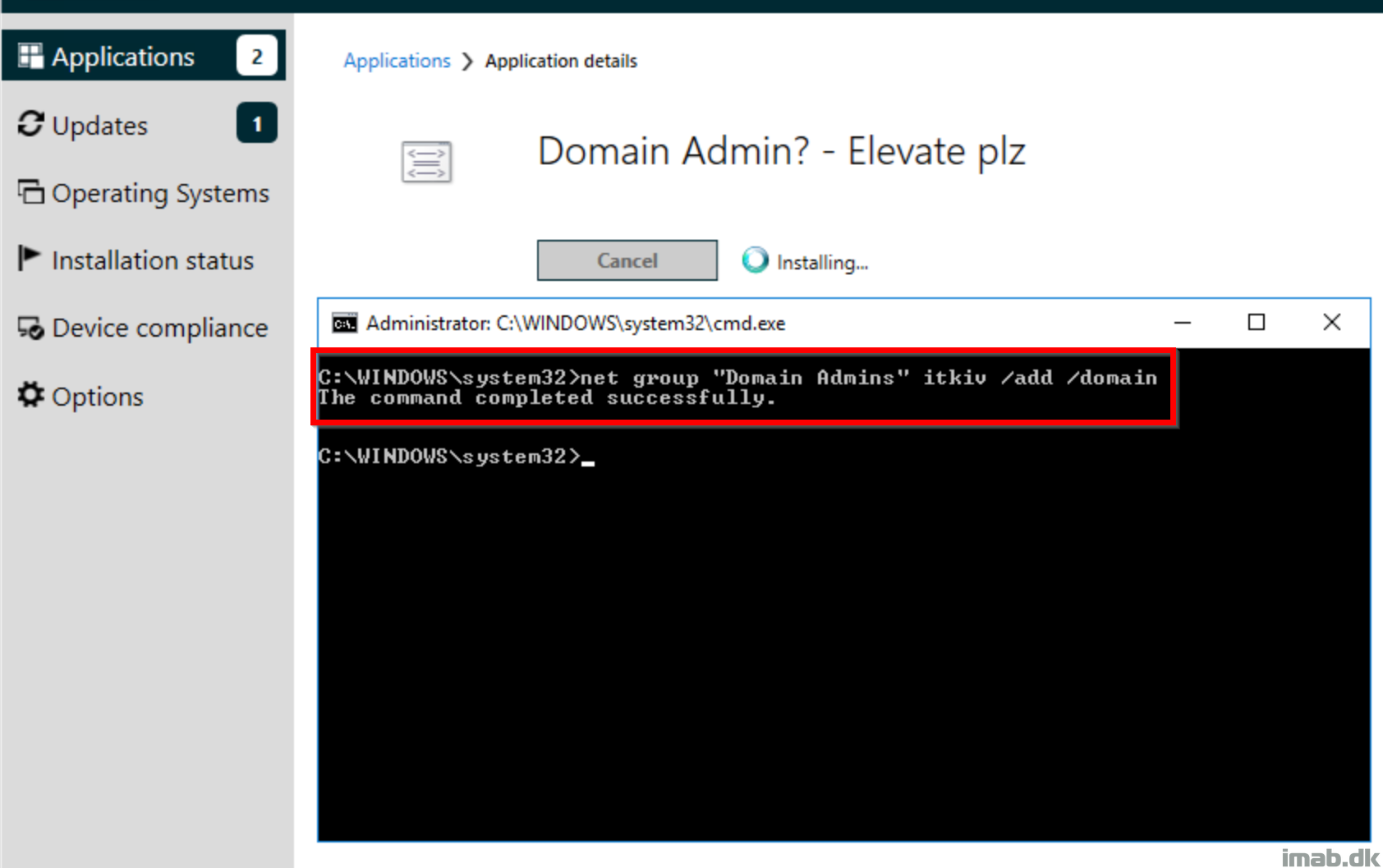
Running a program similar to above via ConfigMgr, is translated into running in SYSTEM context.
Running anything as SYSTEM on a Domain Controller is similar to being Domain Admin. From there, you are free to run ‘net group “Domain Admins” <username> /add /domain’ to add whoever you wish into the Domain Admins group.
Domain Admins membership compliance?
Want to make sure, that no one is becoming Domain Admin by chance?
Take a look on me and my colleagues post here: Automatically remove and disable unwelcome objects from privileged on-premises Active Directory groups using Microsoft Sentinel – imab.dk
ENJOY 🙂