Introduction
I accidentally got to spend my entire weekend, toying around and testing the new Endpoint Analytics Proactive Remediations feature in Microsoft Endpoint Manager (Intune).
- New to Endpoint Analytics? Then grab a quick peek at following docs: What is Endpoint analytics (preview)?
Long story short is, that Proactive Remediations is capable of running Powershell scripts on a schedule on your Windows 10 devices, similar to what we have done for years with Configuration Manager and scheduled tasks.
So, I needed my Windows 10 Toast Notification Script to work with this delicious new feature – and now it does, hitting a version of 1.8.0. All the details down below.
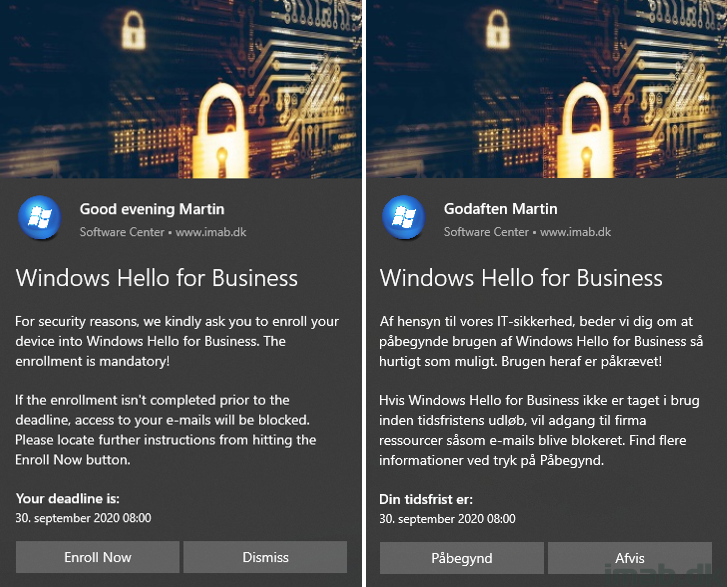
NOTE: You can’t really tell, but the examples below are indeed generated from using Proactive Remediations. My Toast Notification Script is triggered, if a certain device is not enrolled with Windows Hello for Business. Blog post incoming. 🙂
- Apologies for the Danish nonsense. I was testing the multi-language portion (in the script) as well, coming from Proactive Remediations 🙂
What’s New
- 1.8.0 – Added support for using Windows 10 Toast Notification Script with Endpoint Analytics Proactive Remediation
- Added support for having config.xml file hosted online
- Added support for having images used in the script hosted online
Config.xml
Images
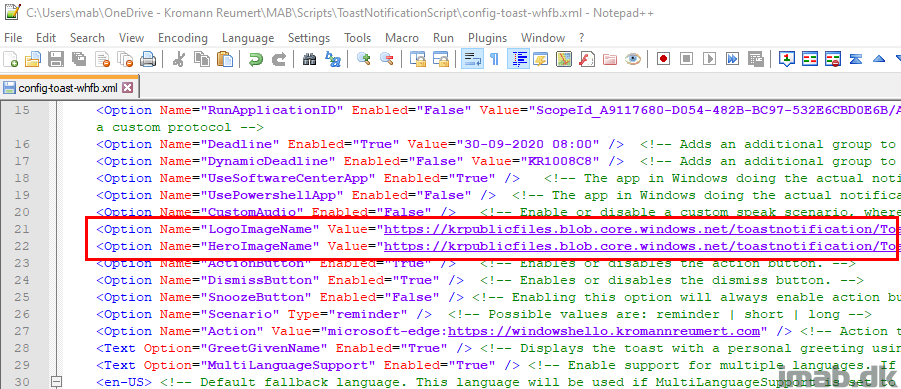
Nothing new is happening to the actual content of the config.xml file. Though I would still like to highlight, that the images can now be hosted on the Internet instead of strictly being local. This is required to have the script working with Proactive Remediations. So far, so good.
In below examples, I have both images hosted in blob storage in Azure:
<Option Name=”LogoImageName” Value=”https://krpublicfiles.blob.core.windows.net/toastnotification/ToastLogoImage.jpg” />
<Option Name=”HeroImageName” Value=”https://krpublicfiles.blob.core.windows.net/toastnotification/ToastHeroImage.jpg” />
Config parameter
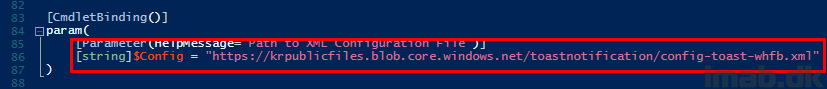
Running my Toast Notification Script with Proactive Remediations requires another small step; hard coding of the config.xml file.
Let me explain: The content of the actual toast is configured through a config file, which again is passed to the script as a parameter.
Proactive Remediations doesn’t support passing parameters to the script, so in order for the Toast Notification Script to work, you will have to hard code the path to the config.xml file.
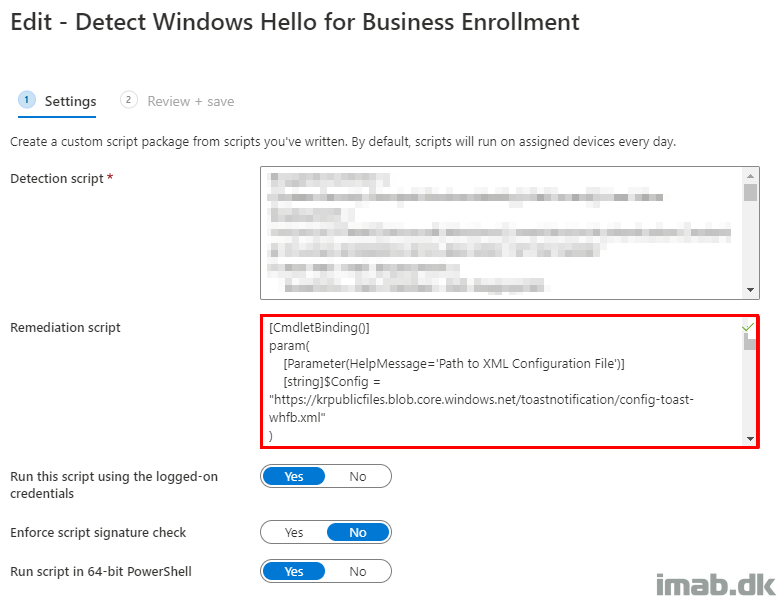
This is easily done in the very beginning of the script. Do something similar to what I have done above and below.
NOTE: Again, the script has been modified to now support config.xml files being hosted online. Here, I’m hosting a config.xml in blob storage in Azure:
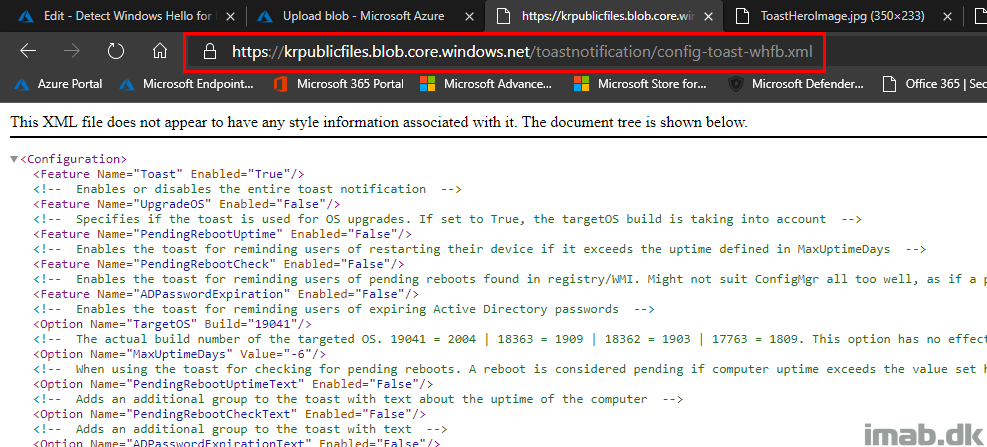
[string]$Config = “https://krpublicfiles.blob.core.windows.net/toastnotification/config-toast-whfb.xml”
The config.xml can be browsed directly from a browser (if one knows the exact URL).
Proactive Remediations
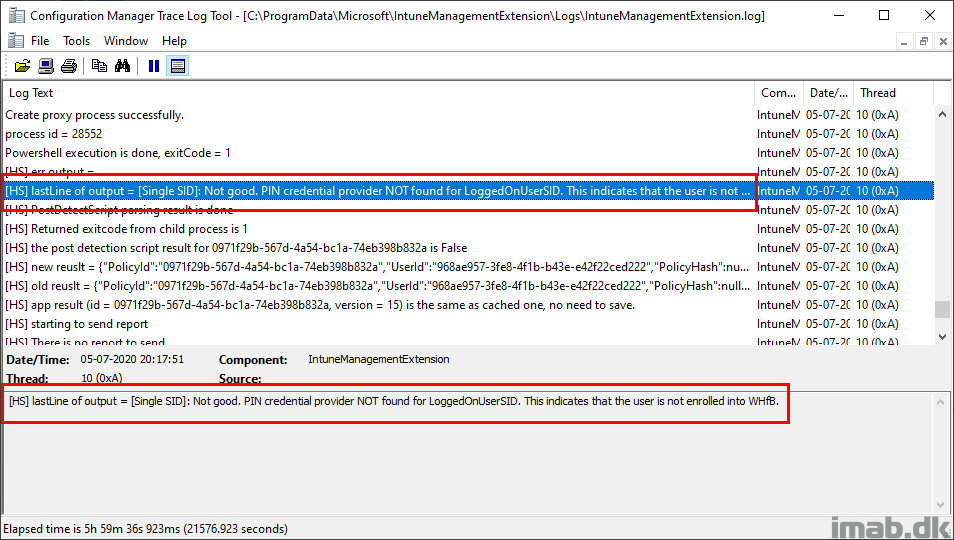
When everything is properly setup (I will go into details in my next blog post), you will see that the detection script finds that my device is not enrolled in Windows Hello for Business (it’s not for testing purposes).
The last line of the output of the detection script is written to the IntuneManagementExtension.log:
[HS] lastLine of output = [Single SID]: Not good. PIN credential provider NOT found for LoggedOnUserSID. This indicates that the user is not enrolled into WHfB.
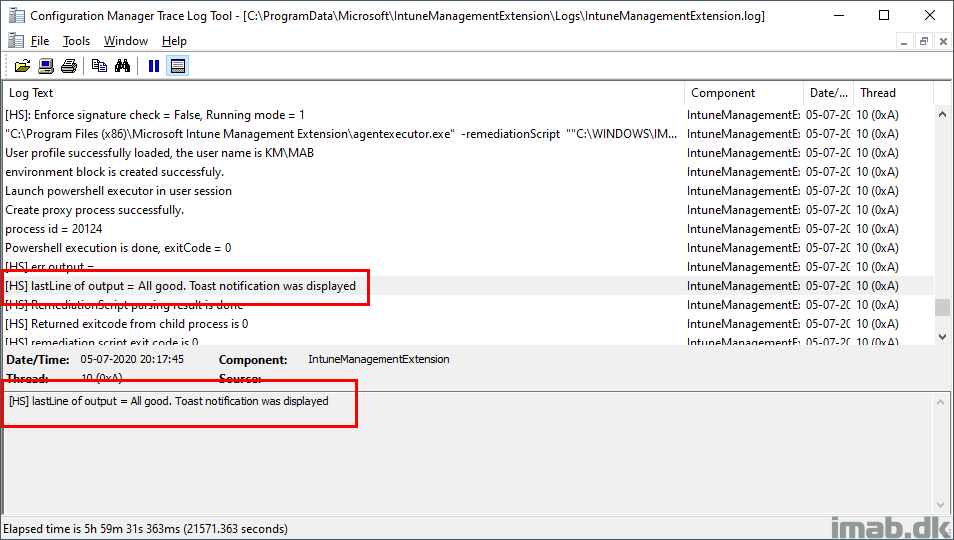
Then comes the remediation script, which essentially is my entire Toast Notification Script pointing to the specific config.xml hosted in Azure blob storage.
Again, last line of the output of the script is written to the IntuneManagementExtension.log:
2020-07-05 21:18:07 INFO: All good. Toast notification was displayed
Pros
The Windows 10 Toast Notification Script still logs its actions to $env:APPDATA\ToastNotificationScript\New-ToastNotification.log when run via Proactive Remediations.
Once the Toast Notification Script has been deployed to Proactive Remediation, it only takes a new upload of the config.xml in order to modify the content of the actual toast notification.
Download
https://github.com/imabdk/Toast-Notification-Script
ENJOY 🙂
I was just going to ask when the amazing Toast Notification script would become available for this kind of situations but you already worked it out. Great stuff again!
Thank you! 🙂
Hi Martin
I was wondering if we can fix the time sync issues on windows 10 devices using the proactive remediation?
I mean if the detection script can check if the device is syncing up correctly with NTP/NT5DS or if there is a time difference.
And with the remediation script we can fix the syncing issue and the device takes the correct time.
Can this be achieved?
Regards,
Moses
Hey Moses, I would assume that’s perfectly doable. 🙂
Hello,
We noticed the greeting time was not working right.
elseif (($Hour -lt 12) -and ($Hour -lt 16)) {
$Greeting = $GreetAfternoonText
we changed “$Hour -lt 12” to “$Hour -gt 12”
I also added the a the write log message as well
Write-Log -Message “Greeting with given name selected. Replacing HeaderText”
$Hour = (Get-Date).TimeOfDay.Hours
if (($Hour -lt 0) -and ($Hour -lt 12)) {
$Greeting = $GreetMorningText
Write-Log -Message “Greeting with Morning Text”
}
elseif (($Hour -lt 12) -and ($Hour -lt 16)) {
$Greeting = $GreetAfternoonText
Write-Log -Message “Greeting with Afternoon Text”
}
else {
$Greeting = $GreetEveningText
write-Log -Message “Greeting with Evening Text”
}
Woops, that is surely a mistake in my end. I was actively rewriting some of that and that’s obviously not correct. Thanks for making me aware 🙂
Hi,
Maybe I missed it but base on the script, only notification check as to see if it’s enabled or not, what if a user disable notification per app for example in this case PowerShell, how can we enable that?
Maybe im a bit confused in this part, or not entirely sure how this goes, but which part of this config goes into the detection script, and which part goes into remediation script? do i upload the “New-ToastNotification.ps1” to both places, with a hardcode link to the xml file. I cant find any details as to this part to make sure im doing it the correct way…
Maybe include these files in future releases, as now you have to upload them to Endpoint Analytics aswell when creating the package.
The detection script depends on what you’re looking to remediate. This post in particular is not discussing that topic, but just how you can use the proactive remediations feature to display toast notifications as well.
Perhaps this post will give a better understanding. I have included the detection script as well in that post. 🙂 https://www.imab.dk/endpoint-analytics-find-devices-not-enrolled-with-windows-hello-for-business/
I am using this toast notification and wanted to disable dismiss button. Any one know how to disable dismiss button?
You do that through the config.xml. DismissButtonEnabled False
Hello,
When I run toast notification from network location, only 2 rows displaying “Software Center” + “New Notification”
nothing more
When I run the same from local, all is good
What can be a problem?
Don’t run the actual script from an UNC path. It’s okay to reference the config.xml from an UNC path. How are you running the script from an UNC path anyhow? Do you use ConfigMgr?
Hello, great script at all ! Support for hosting the pictures on a network share (similar to hosting it online) would be great. Then the script could also be used for a Configuration Baseline in MEMCM (which works in the same way as the Proactive Remediation in Inutune with a discovery and remediation script). Adding the XML file on a network share already works – but unfortunately not the pictures.
Hello. Our users do not have local admin rights on their systems. Do any additional steps need to be taken in this case?
No, the script does not require the user to be local admin 🙂
Hello, is it possible to send a toast if I only want to send a global message to a group in Intune?
Hi there, this looks great.
Are we able to use it to call an available Intune app install like we can with SCCM? This is what we mainly use your toast for.
Thanks, Phil.
This is awesome! Well done. Any way that we can check and prevent it from displaying multiple notifications? My example is using your powershell method as a remediation hourly and if the user goes away for the weekend, they come back to multiple toast notifications. Can I somehow prevent the extras?
Hello Martin
Looked at your script and its what we have been looking for. Questions i have are.
1. any special settings needed in the blob storage?
2. Is it just the xml and images that need to be uploaded to the blob storage?
3. Is the remediation the same for all xml as i will be using the reboot needed option.?