Introduction
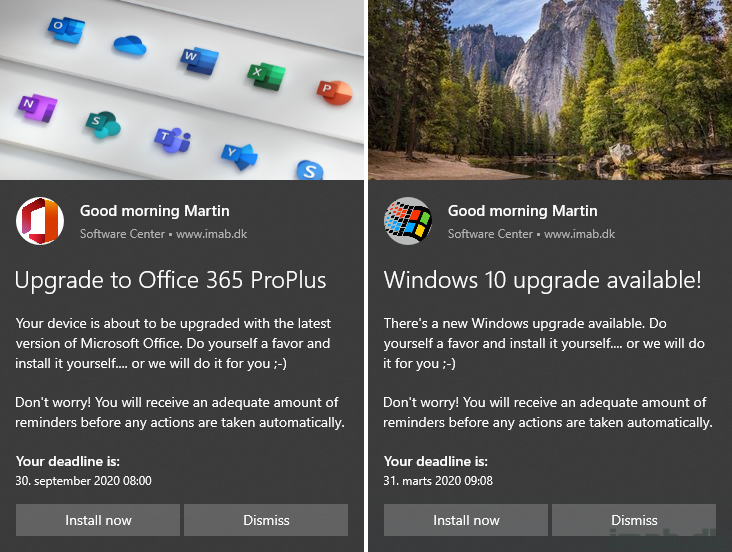
OK, so this post is admittedly a few weeks overdue, but regardless still relevant. Microsoft has decided, as we know by now, to carry out a name change of the Office 365 ProPlus suite, and rename the product to Microsoft 365 Apps (for Enterprise).
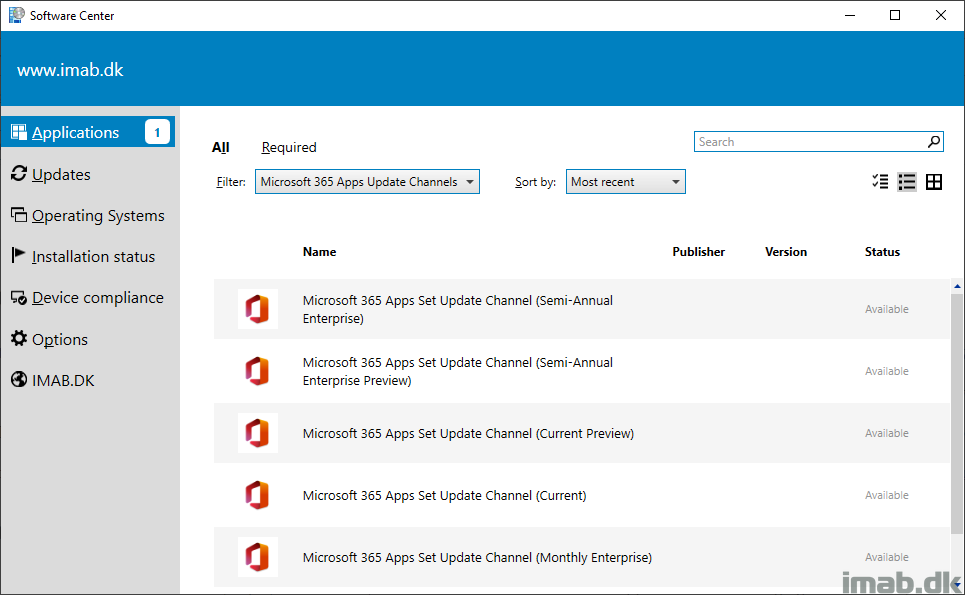
Following this change of name, Microsoft also decided to introduce some new changes to the update channels, which includes new names as well as a brand new update channel: Monthly Enterprise Channel.
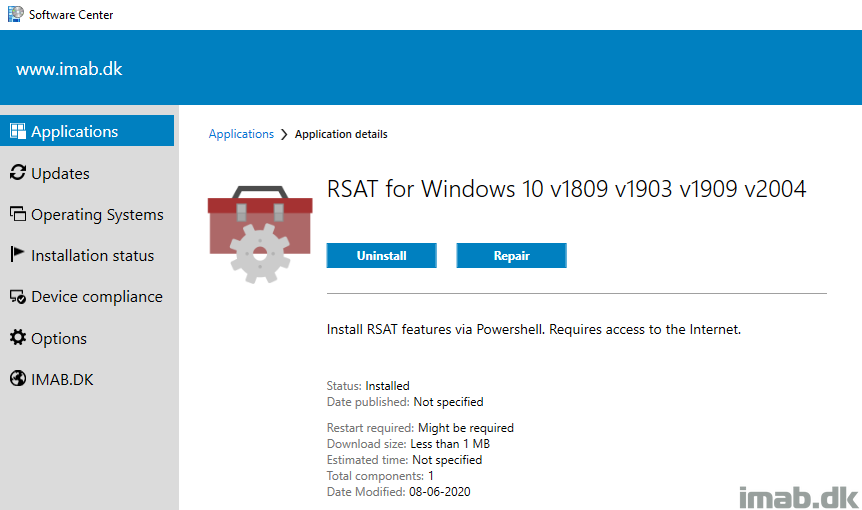
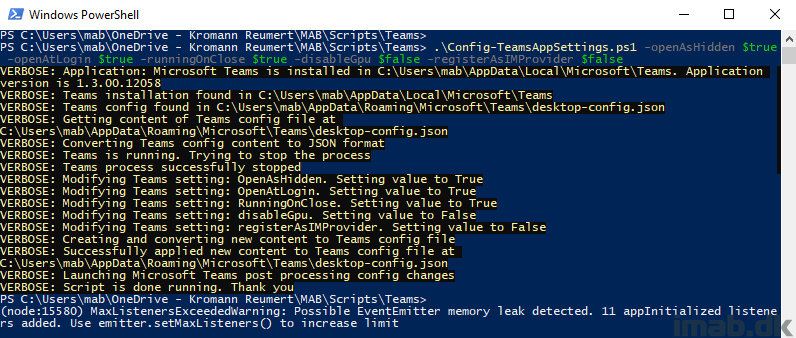
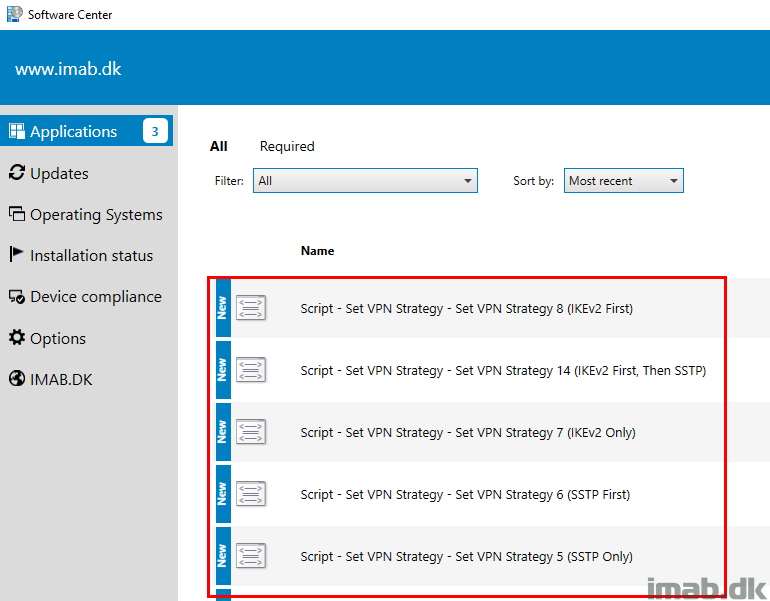
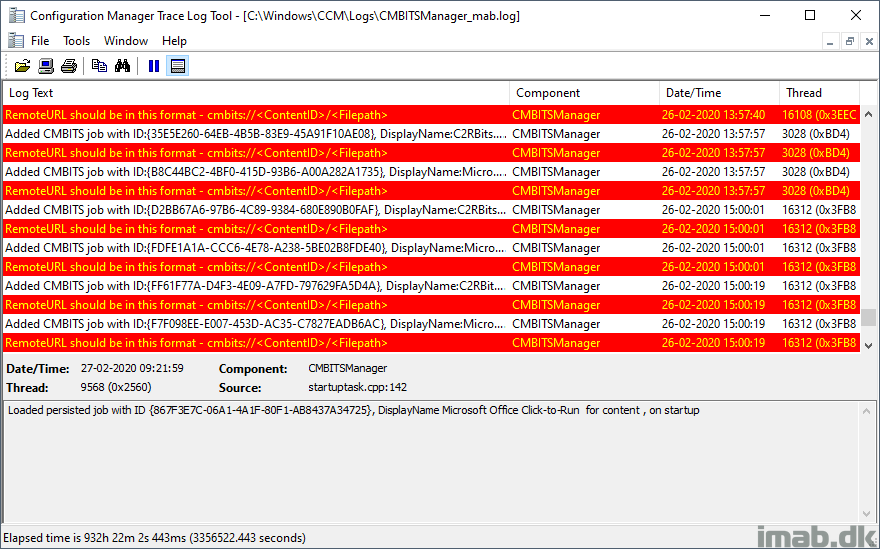
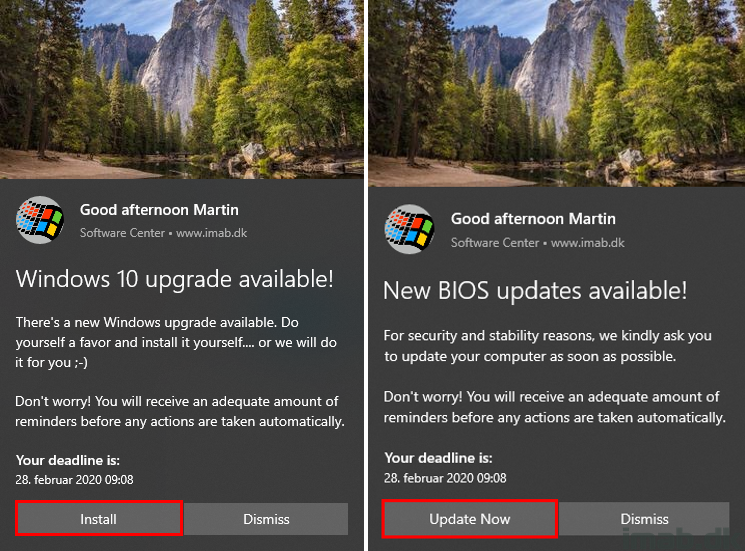
So I figured, all things taken into considerations, that I wanted to go into details on how I’m changing the update channels using Configuration Manager.
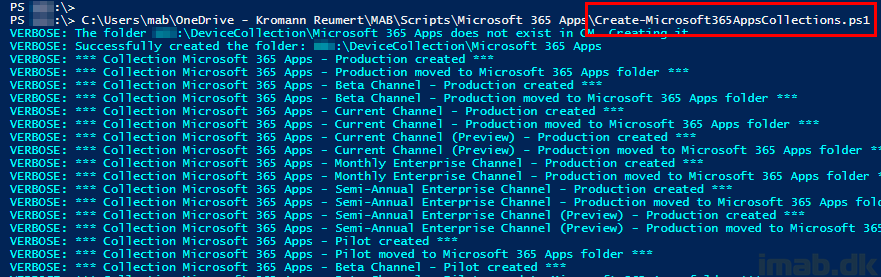
This is a somewhat continuation of my previous blog post: Use Powershell to create device collections in Configuration Manager for the new Microsoft 365 Apps update channels
Carrot on a stick: All of the configurations I have made for this setup, I have exported for you to download. No real configuration needed in your end. Just download and import – almost. 😀